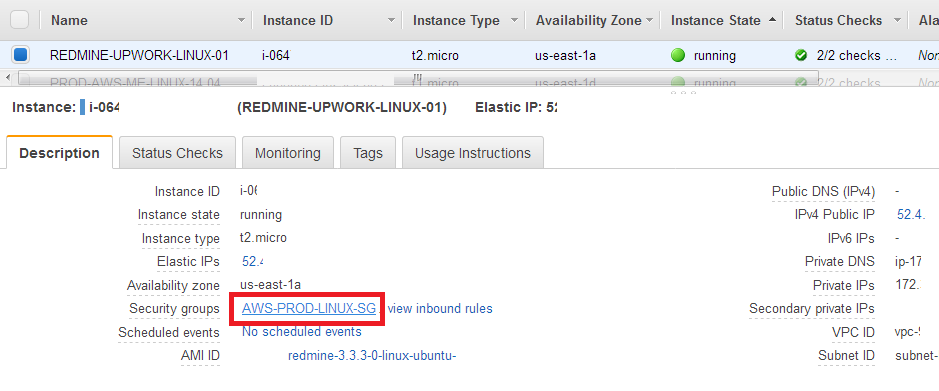
Note: The above image shows an EC2 server selected in the AWS console, and in the description a link to the security group that is attached. Clicking that link takes you to the security group.
After you configure and deploy your new aMiSTACX stack, don’t forget to restrict access to the SSH port. That’s the reminder the AWS console EC2 deployment shows when you launch an EC2 with SSH set to 0.0.0.0/0; that it’s open to the world.
A basic way to resolve this in two simple steps:
1. Type in your browser search; “What is my IP address”
2. Copy the result into the AWS security Group that is responsible for the EC2 sever, and specifically the SSH port. Simply click edit, paste, and add append a “/”at the end so that AWS presents an automatic CIDR format for the IP address.
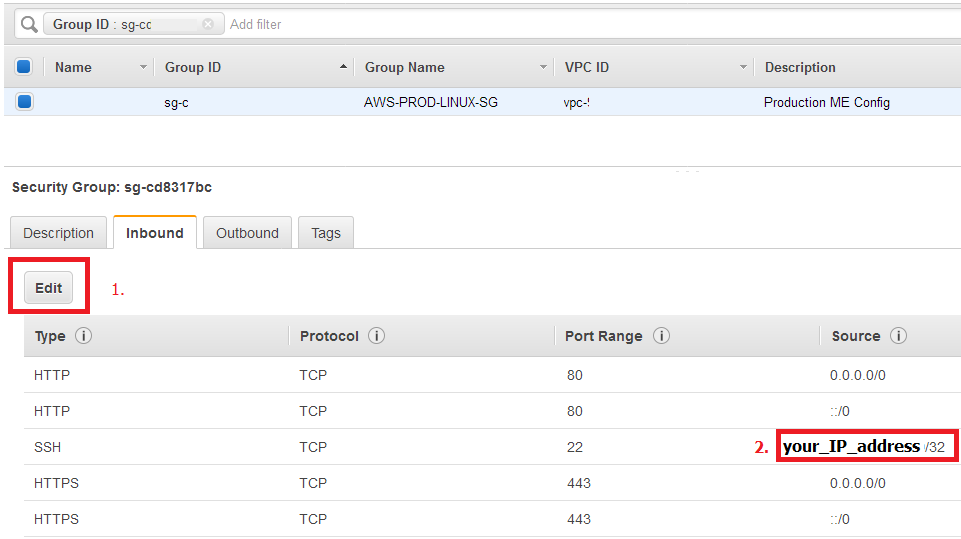
Keep in perspective this only works for static IP addresses.
In the simplest form, AWS security groups allow a little peace of mind.
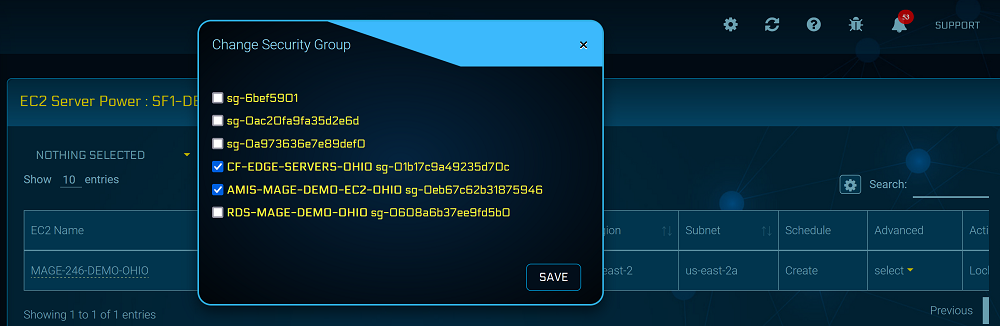
Tip! You can manage security groups from A51, and if you set Cloudflare to always HTTPS, you can close port 80 until you need it.
Secured Systems
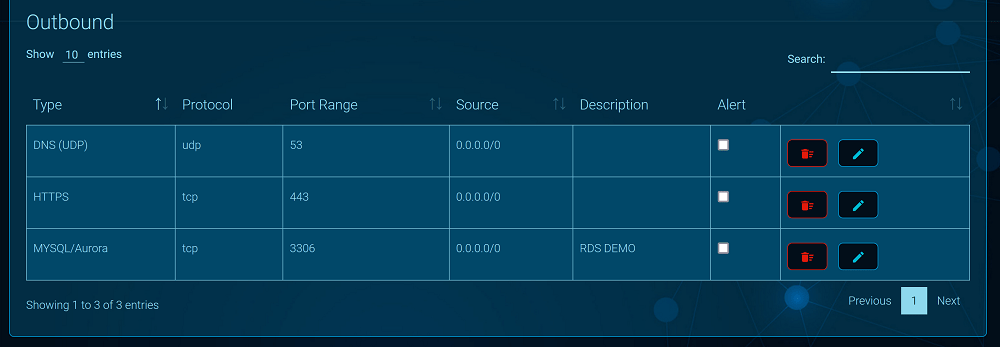
A secured production system will have access to 443 only via your CDN’s IP addresses [or load-balancer]. We normally use Cloudflare, so our security group has the edge server IP addresses attached as a separate policy.
Port 80 is closed, and port 8080 is restricted to a single admin IP address; SSH and Solr are also restricted.
Outbound SGs are also locked down, and we remove the default “All Traffic”, and only allow 443, 80, 53 UDP; however, you may also need to add your SMTP server, RDS port 3306, and/or an SSH port 22. It will all depend on your specific requirements.
As shown above, A51 makes managing security groups easy. There are many advanced functions available such as find and replace, and copy an SG from a template. You can also send yourself an alert that you made a change to the SG. A perfect reminder during testing!
RDS Security Group
If you deployed your server with an RDS database option, you will want to verify that the AWS security group as a basic level of security. By default this means, not set to public, and that communication is ONLY from the private IP address of the parent EC2.
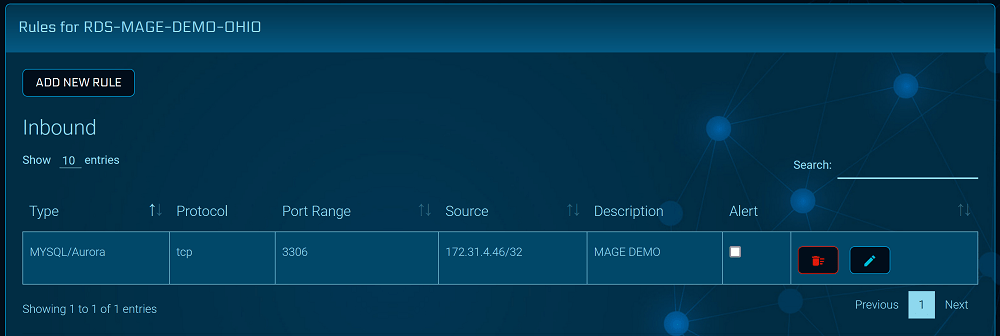
A51 makes this easier to verify, as there is a “details” option in the advanced power menu that will list your private IP address. This will be the same IP address found in the RDS security group. As shown in the example image above.
It’s all up to YOU!
Although aMiSTACX provides a basic level of default deployment security, it is up to you to make sure all systems are secured according to your environment and your needs. Please review our post deployment checklist for more tips.
~Lead_Robot