Cloudflare WAF Rule to restrict URL access
Warning! Improper application of this rule can block traffic to your site. Test with a VPN and/or IP addresses not in your list.
Setting up Two-Factor Authentication [2FA] is a pain for many applications that involve multiple administrators. A simple alternative that leverages Cloudflare’s Web Access Firewall [WAF] is to restrict access to a URL path by an IP address list.
In our example, we will restrict access to our Admin Panel for or demo deployment of Magento 2.4.6 Open Source. Here is the URL path:
https://mage.amistacxdemos.io/admin_b01ved
The first step is to create an IP list that contains your approved IP Addresses that will access the URL. All other IP addresses will be blocked.
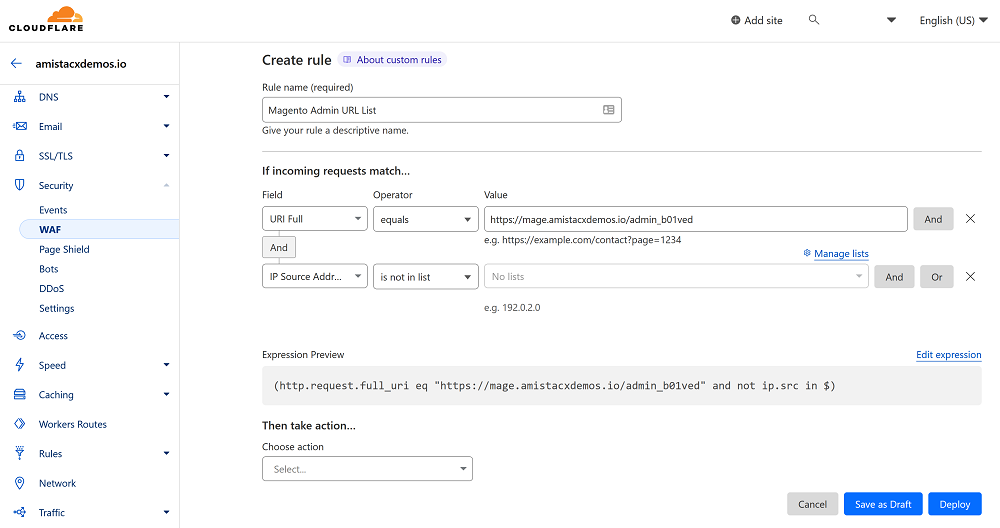
From the WAF section, select Create Rule. Name and put the full path to your rule. Put an AND logic condition, and then set IP Source Address “is not in list”, and specify your approved list.
For the Choose Action, select Block, and then Deploy it.
Important! If this rule is not set up correctly, you could block traffic to your entire domain.
Note: Another effect way to manage admin URL access is to use a Cloudflare Rate Limiting Rule.
Cloudflare Managed Lists
They are hard to find, so it is best to follow the Manage Lists URL in the WAF rule.
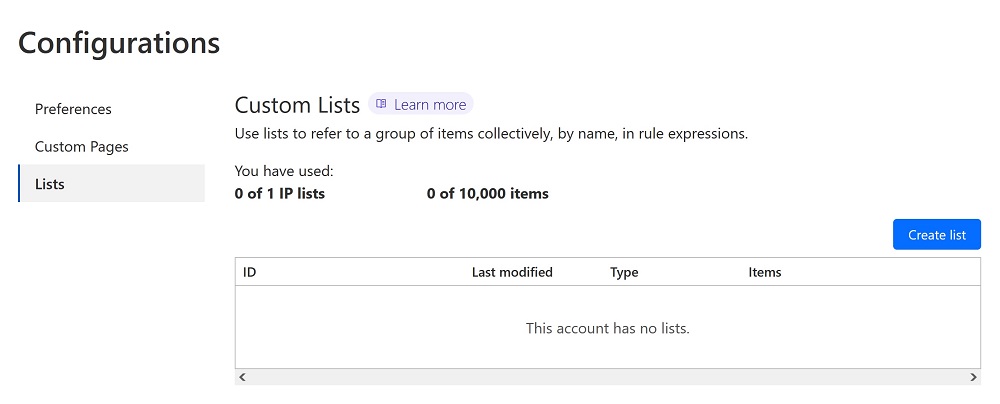
Create a new custom list.
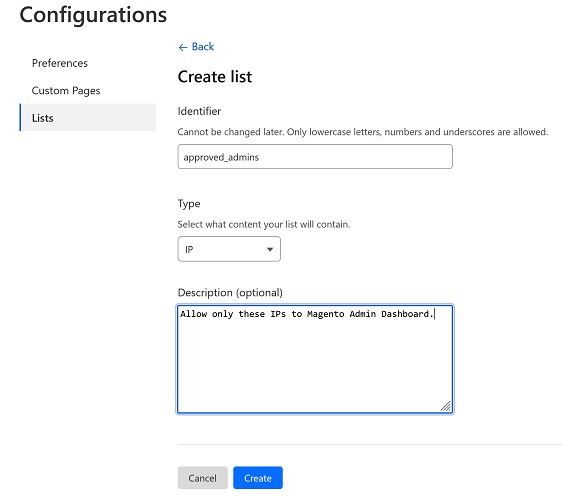
Name and provide an description, and select IP as the content. These will be your IP addresses that are approved.
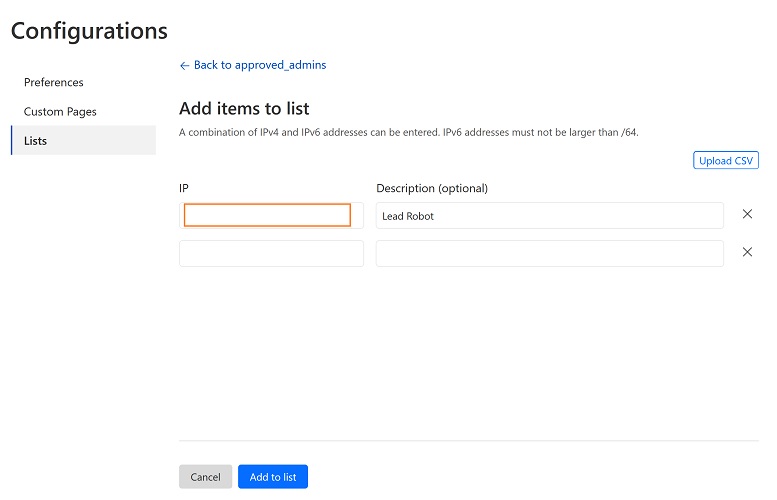
Add one or more IP addresses to your new list.
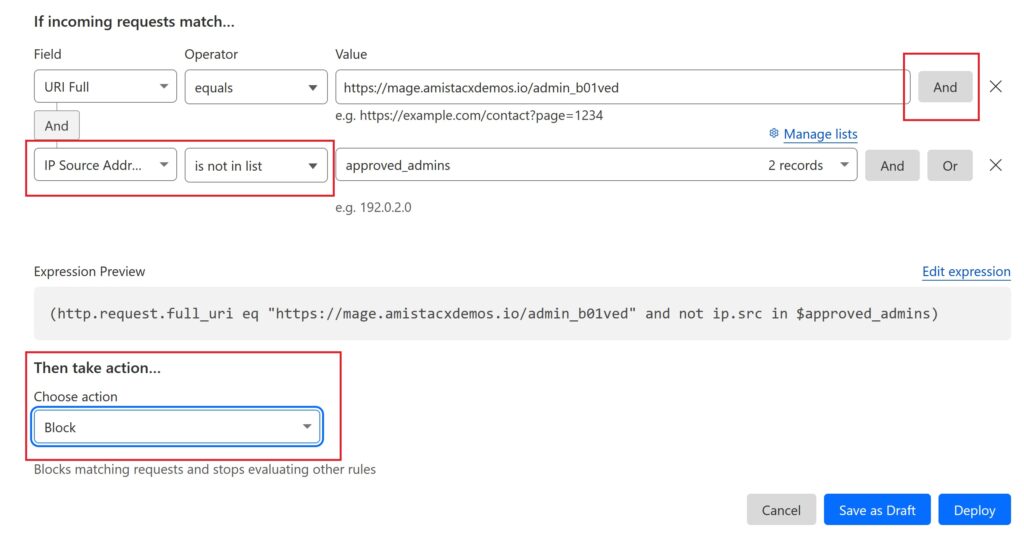
Here you can see I added our new Custom List called approved_admins to my WAF rule. I also have the selected action as block. Deploy the new WAF rule.
Can’t stress this enough to check the final product with a VPN and/or alternative IP addresses; otherwise, you may block traffic to your entire domain.
If you test the URL in this post, you will see you will reach a Cloudflare Block page. You will also notice, you can still access the root domain.
A very simple way to avoid using 2FA with Magento or WordPress that could lead to denial of service for you or your team.
~Lead_Robot